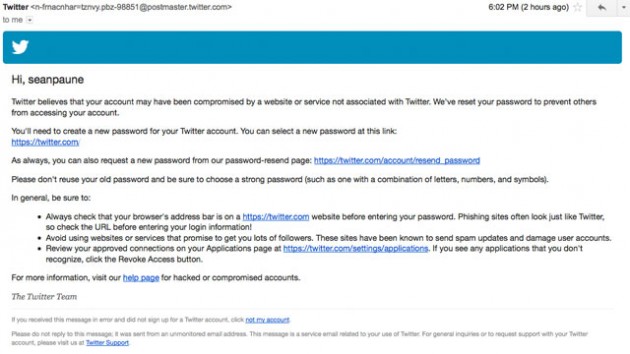
Soon after word hit about the unbelievably easy Apple ID exploit, Apple has responded by saying it’s already working on a fix. As it should be. If it’s not happening on the mobile side, issues are springing up elsewhere.
Soon after word hit about the unbelievably easy Apple ID exploit, Apple has responded by saying it’s already working on a fix. As it should be. If it’s not happening on the mobile side, issues are springing up elsewhere.
In a statement to The Verge, the company lamented the glaring issue and said it takescustomer privacy very seriously. Let’s hope Apple can tie this one up quick, too. All someone needs to take control of someone else’s Apple ID is their email and date of birth—you can get that kind of information on Facebook very easily.
As of now, Apple has taken down its iForgot password reset tool as a temporary solution. That might be an acceptable short-term fix, but in the long run, let’s hope Apple develops a stricter protocol when reseting a password. Apple IDs are the key to Apple’s content kingdom; if user IDs start running rampant, who knows what kind of backlash the company will face.
[Source: TechnoBuffalo]